Chpater 5 Cisco 1 Reading Organizer Answers
CCNA 1 Chapter five v5.1 + v6.0 Examination Online 2018-2019
Mar 17, 2016 Last Updated: Feb 12, 2019 CCNA ane Test Online
0 of 25 questions completed
Questions:
- 1
- 2
- 3
- 4
- five
- 6
- 7
- 8
- ix
- ten
- eleven
- 12
- thirteen
- xiv
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
Information
You accept already completed the quiz earlier. Hence y'all tin non start it again.
Quiz is loading...
You must sign in or sign upward to first the quiz.
Yous have to finish following quiz, to commencement this quiz:
0 of 25 questions answered correctly
Your time:
Fourth dimension has elapsed
You have reached 0 of 0 points, (0)
Categories
- Non categorized 0%
- i
- ii
- 3
- 4
- v
- half dozen
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- fifteen
- 16
- 17
- 18
- nineteen
- twenty
- 21
- 22
- 23
- 24
- 25
- Answered
- Review
-
Question 1 of 25
ane pointsWhat happens to runt frames received past a Cisco Ethernet switch?
In an attempt to conserve bandwidth and not forward useless frames, Ethernet devices drop frames that are considered to be runt (less than 64 bytes) or jumbo (greater than 1500 bytes) frames.
-
Question 2 of 25
1 pointsWhat are the ii sizes (minimum and maximum) of an Ethernet frame? (Cull two.)
The minimum Ethernet frame is 64 bytes. The maximum Ethernet frame is 1518 bytes. A network technician must know the minimum and maximum frame size in order to recognize runt and jumbo frames.
-
Question three of 25
1 pointsWhat statement describes Ethernet?
Ethernet is the most common LAN protocol in the world. Information technology operates at Layer 1 and two, but is not required for Internet advice. The OSI model is used to describe how networks operate. A WAN connects multiple sites located in different countries.
-
Question iv of 25
i pointsWhich ii statements depict features or functions of the logical link control sublayer in Ethernet standards? (Cull ii.)
Logical link command is implemented in software and enables the data link layer to communicate with the upper layers of the protocol suite. Logical link control is specified in the IEEE 802.2 standard. IEEE 802.3 is a suite of standards that define the unlike Ethernet types. The MAC (Media Admission Control) sublayer is responsible for the placement and retrieval of frames on and off the media. The MAC sublayer is also responsible for adding a header and a trailer to the network layer protocol data unit (PDU).
-
Question five of 25
1 pointsWhat statement describes a characteristic of MAC addresses?
Whatsoever vendor selling Ethernet devices must annals with the IEEE to ensure the vendor is assigned a unique 24-bit code, which becomes the first 24 bits of the MAC accost. The last 24 bits of the MAC address are generated per hardware device. This helps to ensure globally unique addresses for each Ethernet device.
-
Question 6 of 25
1 pointsWhich statement is true about MAC addresses?
A MAC address is composed of 6 bytes. The first iii bytes are used for vendor identification and the last 3 bytes must be assigned a unique value within the aforementioned OUI. MAC addresses are implemented in hardware. A NIC needs a MAC accost to communicate over the LAN. The IEEE regulates the MAC addresses.
-
Question 7 of 25
one pointsWhich destination address is used in an ARP asking frame?
The purpose of an ARP request is to find the MAC address of the destination host on an Ethernet LAN. The ARP process sends a Layer two broadcast to all devices on the Ethernet LAN. The frame contains the IP address of the destination and the circulate MAC address, FFFF.FFFF.FFFF.
-
Question 8 of 25
1 pointsWhat addressing information is recorded by a switch to build its MAC address table?
A switch builds a MAC address tabular array by inspecting incoming Layer 2 frames and recording the source MAC address plant in the frame header. The discovered and recorded MAC address is then associated with the port used to receive the frame.
-
Question 9 of 25
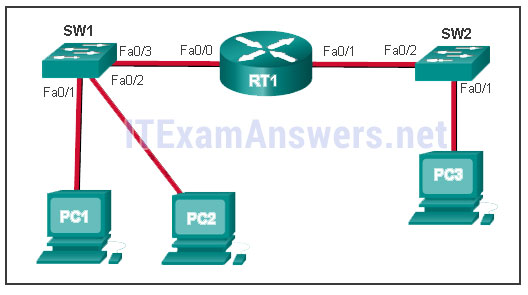
i pointsRefer to the exhibit. The exhibit shows a small switched network and the contents of the MAC address table of the switch. PC1 has sent a frame addressed to PC3. What will the switch do with the frame?

The MAC address of PC3 is non nowadays in the MAC tabular array of the switch. Because the switch does not know where to ship the frame that is addressed to PC3, it will forward the frame to all the switch ports, except for port 4, which is the incoming port.
-
Question 10 of 25
1 pointsWhich switching method uses the CRC value in a frame?
When the shop-and-forward switching method is used, the switch receives the consummate frame earlier forwarding information technology on to the destination. The cyclic redundancy check (CRC) office of the trailer is used to determine if the frame has been modified during transit. In contrast, a cutting-through switch forwards the frame once the destination Layer two address is read. Two types of cut-through switching methods are fast-forward and fragment-free.
-
Question 11 of 25
one pointsWhat is auto-MDIX?
Car-MDIX is a feature that is enabled on the latest Cisco switches and that allows the switch to discover and use whatever blazon of cable is attached to a specific port.
-
Question 12 of 25
1 pointsRefer to the exhibit. PC1 issues an ARP asking because it needs to send a bundle to PC2. In this scenario, what will happen next?
When a network device wants to communicate with another device on the aforementioned network, information technology sends a circulate ARP asking. In this instance, the asking will contain the IP address of PC2. The destination device (PC2) sends an ARP respond with its MAC address.
-
Question 13 of 25
1 pointsWhat are two potential network problems that tin event from ARP operation? (Choose 2.)
Large numbers of ARP circulate messages could crusade momentary information communications delays. Network attackers could manipulate MAC address and IP address mappings in ARP messages with the intent to intercept network traffic. ARP requests and replies crusade entries to be made into the ARP table, non the MAC address table. ARP tabular array overflows are very unlikely. Manually configuring static ARP associations is a style to prevent, not facilitate, ARP poisoning and MAC address spoofing. Multiple ARP replies resulting in the switch MAC address table containing entries that friction match the MAC addresses of connected nodes and are associated with the relevant switch port are required for normal switch frame forwarding operations. It is not an ARP caused network problem.
-
Question 14 of 25
1 pointsFill in the blank.
- A collision fragment, also known as a (RUNT) frame, is a frame of fewer than 64 bytes in length.
A runt frame is a frame of fewer than 64 bytes, usually generated by a collision or a network interface failure.
-
Question 15 of 25
1 pointsFill in the blank.
- On a Cisco switch, (port-based) memory buffering is used to buffer frames in queues linked to specific incoming and outgoing ports.
-
Question 16 of 25
1 pointsFill in the blank.
- ARP (spoofing) is a technique that is used to send imitation ARP messages to other hosts in the LAN. The aim is to associate IP addresses to the wrong MAC addresses.
ARP spoofing or ARP poisoning is a technique used by an attacker to reply to an ARP request for an IPv4 accost belonging to another device, such as the default gateway.
-
Question 17 of 25
one pointsWhich argument describes the treatment of ARP requests on the local link?
-
Question 18 of 25
1 pointsRefer to the exhibit.
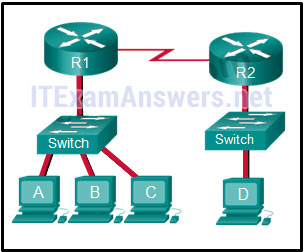 The switches are in their default configuration. Host A needs to communicate with host D, but host A does non have the MAC address for its default gateway. Which network hosts volition receive the ARP request sent by host A?
The switches are in their default configuration. Host A needs to communicate with host D, but host A does non have the MAC address for its default gateway. Which network hosts volition receive the ARP request sent by host A?Since host A does not take the MAC address of the default gateway in its ARP table, host A sends an ARP circulate. The ARP broadcast would exist sent to every device on the local network. Hosts B, C, and router R1 would receive the broadcast. Router R1 would not forward the message.
-
Question 19 of 25
1 pointsRefer to the showroom.
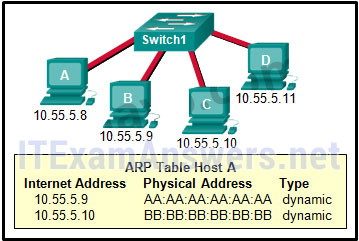 A switch with a default configuration connects 4 hosts. The ARP table for host A is shown. What happens when host A wants to transport an IP packet to host D?
A switch with a default configuration connects 4 hosts. The ARP table for host A is shown. What happens when host A wants to transport an IP packet to host D?Whenever the destination MAC address is not contained within the ARP table of the originating host, the host (host A in this instance) will ship a Layer 2 broadcast that has a destination MAC accost of FF:FF:FF:FF:FF:FF. All devices on the same network receive this broadcast. Host D will respond to this broadcast.
-
Question twenty of 25
1 pointsTrue or False? When a device is sending data to another device on a remote network, the Ethernet frame is sent to the MAC address of the default gateway.
A MAC address is just useful on the local Ethernet network. When data is destined for a remote network of any type, the information is sent to the default gateway device, the Layer 3 device that routes for the local network.
-
Question 21 of 25
1 pointsThe ARP table in a switch maps which two types of accost together?
The switch ARP tabular array keeps a mapping of Layer ii MAC addresses to Layer 3 IP addresses. These mappings can be learned by the switch dynamically through ARP or statically through manual configuration.
-
Question 22 of 25
1 pointsLucifer the characteristic to the forwarding method. (Not all options are used.)
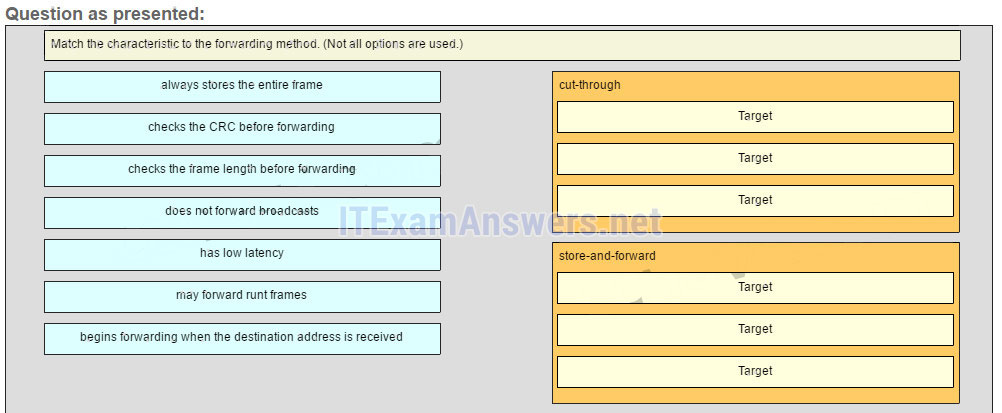
- low latency (A)
- may forward runt frames (B)
- begins forwarding when the destination accost is received (C)
- e'er stores the entire frame (D)
- checks the CRC before forwarding (East)
- checks the frame length before forwarding (F)
- does not forward broadcasts
A store-and-frontwards switch always stores the entire frame before forwarding, and checks its CRC and frame length. A cut-through switch can forward frames before receiving the destination accost field, thus presenting less latency than a store-and-frontward switch. Because the frame can begin to be forwarded earlier information technology is completely received, the switch may transmit a corrupt or runt frame. All forwarding methods require a Layer 2 switch to forward broadcast frames.
-
Question 23 of 25
1 pointsWhat is the aim of an ARP spoofing attack?
-
Question 24 of 25
1 pointsWhat is a characteristic of port-based retentiveness buffering?
Buffering is a technique used by Ethernet switches to store frames until they can be transmitted. With port-based buffering, frames are stored in queues that are linked to specific incoming and outgoing ports.
-
Question 25 of 25
1 pointsWhat is the minimum Ethernet frame size that will not be discarded by the receiver equally a runt frame?
Related Manufactures

Source: https://itexamanswers.net/ccna-1-chapter-5-v5-1-v6-0-test-online.html
Post a Comment for "Chpater 5 Cisco 1 Reading Organizer Answers"